Editor’s Note: What follows connects the dots across three domains that are now inseparable: cybersecurity operations facing a fast-moving surge of hacktivist and state-linked activity; information governance teams navigating data residency rules that presume stable geography; and eDiscovery leaders confronting preservation and production obligations when access can vanish overnight through outages, internet shutdowns, or physical destruction. The analysis also surfaces an emerging fault line in cyber insurance—especially war exclusions—at the exact moment cloud infrastructure risk modeling is being rewritten in real time. Amid the technical and legal implications, the human cost remains central: casualties and injuries among migrant workers underscore duty-of-care and workforce continuity obligations that organizations cannot relegate to policy language.
Industry News – Cybersecurity Beat
Cybersecurity Implications of the 2026 Middle East Escalation: When Cloud Infrastructure Becomes a Target
ComplexDiscovery Staff
Editor’s Disclaimer: This report reflects corroborated reporting as of 7:00 AM CST, March 3, 2026. Following the publication of initial reports, Amazon Web Services (AWS) stated via official service health communications that unidentified objects struck at least one data center in its Middle East (UAE) Region (ME-CENTRAL-1), causing a fire and a localized power loss in one Availability Zone and related disruption in another, with secondary service impacts reported in its Middle East (Bahrain) Region (ME-SOUTH-1). The underlying conflict remains highly volatile; casualty figures, physical damage assessments, and associated cyber threat intelligence may shift rapidly. ComplexDiscovery continues to monitor official disclosures from the UAE Ministry of Defence, the UK’s National Cyber Security Centre (NCSC), and AWS Health dashboards. Readers are advised that any potential “force majeure” determinations or regulatory relief regarding regional data residency obligations under UAE Federal Decree-Law No. 45 of 2021 (UAE PDPL) remain, as of this report, unannounced by UAE authorities.
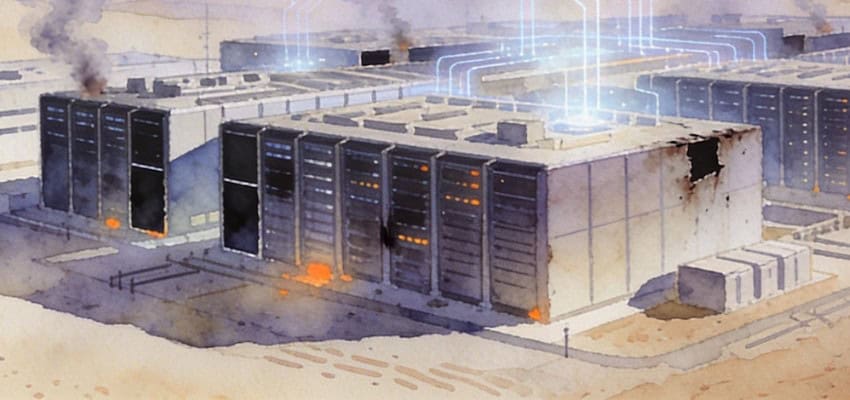
On March 1, 2026, a fire broke out inside an Amazon Web Services data center in the United Arab Emirates after unidentified objects struck the facility—marking what appears to be the first time a major American tech company’s cloud infrastructure was physically damaged by military action, according to Reuters and multiple industry analysts. Within hours, roughly sixty AWS services went dark across the Middle East, according to 404 Media’s reporting on AWS health dashboard data, and Amazon quietly advised customers to migrate workloads to European regions while engineers assessed structural damage, disrupted power systems, and waterlogged server racks from fire suppression efforts.
The strike was no isolated event. It arrived in the immediate aftermath of Operation Epic Fury and Roaring Lion, a coordinated U.S.-Israeli campaign launched on February 28 that targeted Iranian leadership compounds, IRGC military facilities, and nuclear-related infrastructure across Tehran, Isfahan, Qom, and other strategic locations. The operation killed Iran’s Supreme Leader Ayatollah Ali Khamenei, according to multiple confirmed reports from Reuters, the BBC, and U.S. officials who stated that the strike on the Leadership House compound was successful and disrupted senior security communications. Tehran responded with a barrage of ballistic missiles and drones aimed at Israel, U.S. bases in the Gulf, and allied nations, including the UAE, Kuwait, Bahrain, Qatar, and Saudi Arabia. The UAE military intercepted 165 ballistic missiles, two cruise missiles, and 541 drones over two days, according to the UAE Defense Ministry, but thirty-five drones and five projectiles penetrated defenses, as reported by Rest of World, striking airports, a port facility, and an AWS data center serving customers across the government, finance, and enterprise technology sectors.
What makes this escalation distinct from past conflicts in the region is not just its kinetic destruction but the parallel cyber campaign unfolding alongside it—a campaign that some cybersecurity analysts, including researchers at CloudSEK and commentators at Infosecurity Magazine, have described as one of the largest coordinated digital offensives in history. The human cost arrived before the digital cost: three migrant workers—nationals of Pakistan, Nepal, and Bangladesh, according to the UAE Defense Ministry, as reported by TIME and CNN—were killed in the UAE strikes, and fifty-eight others of various nationalities were injured. The Philippines’ Department of Foreign Affairs upgraded its travel advisory for the UAE, Bahrain, Kuwait, Qatar, and Saudi Arabia to a level that automatically triggers a deployment ban on newly hired workers. The International Labor Organization estimates there are over twenty-four million migrant workers in Arab states, as cited by CNN, many housed near industrial zones and infrastructure that became targets. For organizations with regional operations, the duty of care owed to employees, contractors, and supply chain workers in affected areas is now an active governance obligation, not a policy abstraction.
Iran’s internet connectivity plummeted to roughly four percent of normal levels, according to CloudSEK’s situation report citing network monitoring data, a near-total blackout that appears to be a combination of state-imposed shutdowns and external cyber operations. Government services, official media platforms, and parts of the energy and aviation sectors went offline. Meanwhile, over 150 hacktivist incidents were recorded within the first seventy-two hours, according to CloudSEK’s February 27–March 1 situation report, and the number of active hacktivist groups reached an estimated sixty by March 2, according to Palo Alto Networks’ Unit 42 threat brief.
The Convergence of Kinetic and Cyber Warfare
The blending of conventional military strikes with systematic digital disruption represents an evolution in modern warfare that cybersecurity, information governance, and eDiscovery professionals cannot afford to treat as a distant geopolitical story. Palo Alto Networks’ Unit 42 published a threat brief on March 2, noting that Iranian command-and-control degradation has likely fractured the coordination of state-aligned cyber units, potentially leading to autonomous tactical decisions by cells operating outside Iran. That unpredictability, Unit 42 analysts warn, makes the threat landscape harder to model and defend against. Organizations that had calibrated their risk posture around structured, centrally directed Iranian APT campaigns now face the prospect of loosely coordinated, opportunistic attacks from actors with varying levels of sophistication.
Sophos’ threat intelligence team, in a report published on March 1 and cited by Cyber Magazine, warned that a hacktivist persona called Handala Hack, linked to Iran’s Ministry of Intelligence and Security, claimed attacks in Jordan and issued threats against multiple countries in the region on February 28. While such groups often overstate their capabilities, Sophos noted that Handala Hack has historically demonstrated the ability to conduct data theft and deploy wiper malware. A separate group tracked by Unit 42 as DieNet claimed distributed denial-of-service attacks on airports in Bahrain and the UAE, banking infrastructure in Jordan, and Saudi financial websites. These are precisely the types of high-visibility symbolic targets designed to generate immediate public attention, even when the underlying systems remain technically intact.
The UK’s National Cyber Security Centre issued an advisory on March 2 stating that, while the direct cyber threat to Britain had not changed, the indirect risk to organizations with a presence or supply chains in the Middle East had increased. The NCSC urged organizations to review their external attack surface, increase monitoring, and test incident response plans. Jonathon Ellison, the NCSC’s director for national resilience, stated in the advisory that organizations should act now to strengthen their cybersecurity posture rather than wait for the threat to arrive on their doorstep.
Data Centers in the Crosshairs
The physical strike on AWS infrastructure has upended assumptions that underpinned billions of dollars in tech investment. Just weeks earlier, the Gulf had been celebrated as the next frontier for artificial intelligence, with the UAE and Qatar joining the U.S.-led Pax Silica initiative designed to keep advanced chips out of Chinese hands. Microsoft had committed to a fifteen-billion-dollar investment in UAE data centers by 2029. Saudi Arabia and the UAE had positioned themselves as stable alternatives for hyperscale cloud computing, inviting Nvidia, AMD, OpenAI, Cerebras, and others to build capacity in the region.
As the Center for Strategic and International Studies warned just days before the strikes, previous regional adversaries targeted pipelines and refineries in Gulf partner states. In a compute-driven era, those same adversaries could instead target data centers, energy infrastructure supporting compute, and fiber chokepoints. That warning has now materialized. AWS confirmed that two UAE facilities were directly struck, and a Bahrain facility sustained damage from a nearby drone impact. The resulting outages affected EC2 virtual servers, S3 storage, and DynamoDB database services. Recovery timelines stretched beyond twenty-four hours due to the need to repair cooling systems, coordinate with local authorities, and ensure physical safety before restoring power.
For organizations with data residency requirements in the Middle East, disaster recovery plans that assumed regional availability may need wholesale revision. AWS itself recommended that affected customers recover from remote backups in alternate regions, ideally in Europe. That guidance, while practical in the moment, exposes a deeper tension: specific data residency frameworks—including the UAE’s Federal Decree-Law No. 45 of 2021 on personal data protection, the Dubai International Financial Centre’s Data Protection Law, Saudi Arabia’s Personal Data Protection Law, and GDPR obligations binding European companies with Middle Eastern processing operations—may require information to remain within geographic boundaries that are now physically insecure. As of this writing, none of these regulatory authorities has issued emergency guidance addressing whether force majeure exemptions apply to data residency obligations during active military conflict, an absence that itself creates compliance uncertainty for organizations attempting to follow AWS’s advice to migrate workloads to Europe. eDiscovery practitioners managing cross-border litigation or regulatory investigations tied to Middle Eastern operations should immediately assess whether their electronically stored information remains accessible, intact, and defensible.
What This Means for Cybersecurity, IG, and eDiscovery Professionals
The cascade of events over the past week delivers several urgent lessons for professionals at the intersection of cybersecurity, information governance, and legal technology. First, the assumption that cloud infrastructure in politically stable-seeming regions is immune from physical disruption has been permanently retired. Organizations should audit their cloud hosting footprint and confirm that backup and failover architectures span geographically diverse regions, not just multiple availability zones within the same country. If your data lives in a single Middle Eastern region, your business continuity plan has a gap that no amount of software redundancy can fill.
Second, the hacktivist surge underscores that threat actors exploit geopolitical flashpoints with remarkable speed. CloudSEK’s situation report documented over 150 hacktivist incidents within seventy-two hours of the February 28 strikes, targeting government, oil and gas, banking, aviation, and telecommunications sectors. The speed of activation means that security teams cannot rely on reactive postures. CISOs should ensure that threat intelligence feeds are configured to flag geopolitical escalation as a trigger for elevated monitoring, and confirm that their security operations centers are staffed and empowered to escalate anomalous activity during weekends and holidays, when many of these attacks tend to occur.
Third, the Iran conflict has demonstrated that AI-enhanced attacks are no longer theoretical. Multiple reports from cybersecurity firms and analysts, including CloudSEK’s situation report and Forrester Research analyst Allie Mellen’s assessment published by Fortune on March 2, describe generative AI being used to improve phishing realism, scale fraud campaigns, and enhance ransomware social engineering. Organizations should update their security awareness training to reflect these evolving tactics, and incident response playbooks should account for the possibility that AI-generated phishing lures may be far more convincing than what defenders have historically encountered.
Fourth, information governance teams face a new category of risk: the weaponization of internet shutdowns. Iran’s connectivity dropped to between one and four percent of normal levels following the strikes, according to internet monitoring groups NetBlocks and Kentik, building on a pattern of government-imposed blackouts that have persisted since January 2026 protests. For multinational organizations with employees, partners, or data processing operations in countries that practice internet shutdowns, the ability to preserve, collect, and produce electronically stored information on court-ordered timelines may be fundamentally compromised. Counsel involved in cross-border litigation should proactively raise these risks with courts and opposing parties, documenting the force majeure conditions that may prevent timely compliance with discovery obligations.
Fifth, the physical destruction of data center infrastructure raises novel questions about evidence preservation and spoliation. If electronically stored information stored in a Middle Eastern cloud region is lost due to military action, the traditional spoliation analysis—which examines whether a party had a duty to preserve, control over the information, and acted with a culpable state of mind—may need to account for circumstances that no reasonable litigation hold could have anticipated. eDiscovery professionals should document their preservation efforts and the external circumstances affecting data availability in real time, creating a contemporaneous record that can support defensibility arguments if challenged later.
Sixth, the AWS strike has exposed a coverage ambiguity that cyber insurance and risk transfer professionals are only beginning to confront. When a kinetic military strike physically destroys cloud infrastructure, the resulting losses may fall into a gap between a traditional property and casualty policy, a standalone cyber policy, and the war exclusion clauses that both types increasingly contain. Lloyd’s of London has been reviewing war-risk exclusion language in recent years following conflict-related claims tied to Ukraine, and industry analysts have already indicated that the UAE incident may accelerate reassessments of cloud infrastructure risk modeling and pricing. Organizations should not wait for that market recalibration. Risk managers and general counsel should immediately review their cyber policy’s war exclusion language, determine whether kinetic damage to third-party cloud infrastructure is covered or excluded, and confirm whether their property and casualty policies address digital assets hosted by cloud providers in conflict zones. The war exclusion clause has never been invoked on a claim reported under a cyber policy, according to Alliant Specialty, but insurance industry observers note that the AWS data center strike may become the test case that changes that precedent.
Actionable Steps for the Week Ahead
Given the speed at which this conflict is evolving, professionals should take immediate action on several fronts. Review your organization’s cloud architecture to confirm that workloads and backups are distributed across geographically separate regions, with documented failover procedures that have been tested within the last ninety days. Verify that your incident response plan addresses geopolitical escalation as a defined threat scenario, and confirm that your security operations team has clear escalation protocols for state-sponsored or hacktivist activity. Update your threat intelligence subscriptions to include advisories from the NCSC, CISA’s Iran Threat Overview page, and vendors such as Palo Alto Networks, CrowdStrike, Sophos, and CloudSEK, which are actively tracking this conflict’s cyber dimensions.
For information governance and eDiscovery professionals specifically, conduct a rapid inventory of electronically stored information that resides in Middle Eastern cloud regions or is accessible through supply chain partners with regional exposure. If litigation holds are in place that cover data stored in affected regions, document the current status of that data and any access disruptions. Communicate with outside counsel about the potential for court orders or production timelines to be affected by ongoing hostilities. And if your organization does business with entities in Iran or adjacent countries, prepare for the possibility that data flows may be intermittently or permanently disrupted, requiring alternative collection and preservation strategies. Organizations with employees or contractors in affected countries should also assess workforce continuity: if your regional IT staff, local legal counsel, or managed service provider personnel cannot reach their workplaces due to airport closures, infrastructure damage, or security lockdowns, your ability to execute preservation, collection, and incident response activities may be materially impaired. That workforce exposure should be documented and factored into both business continuity plans and any ESG or corporate social responsibility disclosures required by your jurisdiction.
The Iranian government’s effort to build a permanent internet kill switch—reportedly in its final stages with Huawei’s involvement, according to a January 14, 2026, investigation by Iran International—signals what digital rights researchers and cybersecurity analysts warn may become a semi-permanent feature of the regional landscape, not a temporary wartime measure. That development has profound implications for any organization that relies on cross-border data flows involving Iran, and it should prompt a broader conversation about how information governance frameworks account for state-imposed connectivity restrictions.
Planning for a World Where “Uptime” Is a Geopolitical Variable
The events of late February and early March 2026 have compressed what analysts had warned were plausible worst-case scenarios into a single week. A major cloud provider’s physical infrastructure has been damaged by military action. A nation’s internet has been functionally erased. State-sponsored and hacktivist cyber operations are running in parallel with kinetic strikes on a scale not previously documented. And the regulatory and governance frameworks that professionals rely on—from data residency requirements to eDiscovery protocols to business continuity standards—are being stress-tested against conditions they were never designed to address.
CrowdStrike reported on March 1, as cited by CNBC and SecurityWeek, that Iranian-linked hackers have already initiated DDoS and reconnaissance activity that security experts warn may signal further escalation. Microsoft’s annual digital defense report, published in late 2025, noted that Iranian state-linked cyber activity volume remains consistently high, with intelligence services focused on long-term espionage against the critical infrastructure of regional adversaries. Separately, the West Point Lieber Institute’s August 2025 analysis documented a 700 percent surge in Iranian state-sponsored attacks since June 2025. Analysts caution that none of these trends are likely to reverse while hostilities continue.
As organizations recalibrate their defenses, they would do well to remember that the lines between physical security, cybersecurity, and information governance are dissolving. The missile that struck an AWS data center is also, in a very real sense, a challenge to every litigation hold, every data retention policy, and every business continuity plan that assumed the cloud was safe because it was intangible.
As the dust settles and the digital fog lifts, one question demands honest examination from every cybersecurity, information governance, and eDiscovery professional: If a single weekend of conflict can physically destroy cloud infrastructure, trigger hundreds of cyberattacks, and sever an entire country from the internet, is your organization’s risk framework built for the world that actually exists—or the one you hoped would continue?
News Sources
- Situation Report: Middle East Escalation (February 27–March 1, 2026) (CloudSEK)
- Middle East Conflict: The Cybersecurity Impact (Cyber Magazine)
- Missile Attacks and Cyber Hacks: Dual Threats of Modern Warfare (The National)
- Threat Brief: March 2026 Escalation of Cyber Risk Related to Iran (Palo Alto Networks Unit 42)
- Hybrid Middle East Conflict Triggers Surge in Global Cyber Activity (Infosecurity Magazine)
- Amazon Says Drone Strikes Damaged 3 Facilities in UAE and Bahrain (CNBC)
- Amazon Fire in UAE: The End of the Gulf’s Safe AI Promise? (Rest of World)
- NCSC Advises UK Organisations to Take Action Following Conflict in the Middle East (UK National Cyber Security Centre)
- Firewalls and Fault Lines: Cyber War in the Middle East (Lieber Institute, West Point)
- British Organizations Urged to Be Alert to Threat of Iranian Cyberattacks (The Record, Recorded Future News)
- Amazon’s AWS Reports Outage After UAE Data Center Struck by ‘Objects’ (Insurance Journal)
- Iran’s Retaliatory Strikes Challenge Image of Gulf Stability (TIME)
- Live Updates: U.S.-Israel Conflict with Iran Widens (PBS NewsHour)
- Iran’s Internet Blackout Enters Fourth Day Amid Reports of Cyberattacks (CNBC, Citing CrowdStrike)
- Iran Could Use AI to Accelerate Cyberattacks on U.S. and Israeli Critical Infrastructure (Fortune, Citing Forrester Research)
Assisted by GAI and LLM Technologies
Additional Reading
- The Gatekeeper’s Key: How the Conformity Assessment Unlocks the EU AI Market
- EDPB and EDPS Weigh In on the Digital Omnibus: Personal Data, Breach Reporting, and AI Governance
- 2026 AI Safety Report Flags Escalating Threats for Cyber, IG, and eDiscovery Professionals
- The Algorithmic Guardrail: National Defense in the Age of Autonomous Risk
- EU’s Preliminary DSA Findings Put TikTok’s Engagement Design in the Regulatory Crosshairs
- Market Reaction or Overreaction? Anthropic’s Legal Plugin and the Facts So Far
- Moltbook and the Rise of AI-Agent Networks: An Enterprise Governance Wake-Up Call
- From One-Eyed Kings to Collective Sight in Enterprise AI
Source: ComplexDiscovery OÜ
ComplexDiscovery’s mission is to enable clarity for complex decisions by providing independent, data‑driven reporting, research, and commentary that make digital risk, legal technology, and regulatory change more legible for practitioners, policymakers, and business leaders.
The post Cybersecurity Implications of the 2026 Middle East Escalation: When Cloud Infrastructure Becomes a Target appeared first on ComplexDiscovery.